The insideBIGDATA Guide to Data Analytics in Government provides an in-depth overview of the use of data analytics technology in the public sector. Focus is given to how data analytics is being used in the government setting with a number of high-profile use case examples, how the Internet-of-Things is taking a firm hold in helping government agencies collect and find insights in a broadening number of data sources, how government sponsored healthcare and life sciences are expanding, as well as how cybersecurity and data analytics are helping to secure government applications.
 Government Use of Big Data for Cybersecurity
Government Use of Big Data for Cybersecurity
The cybersecurity waters are teeming with threats by criminals, nation states, and hacktivists, and government agencies do not have the personnel, tools, or time to properly handle the massive amounts of data involved especially with the attack surface constantly expanding. However, with the ability to discover insights in the very data they are sinking in, big data may be the requisite lifeline.
While 90 percent of government data analytics users report they have seen a decline in security breaches, 49 percent of federal agencies say cybersecurity compromises occur at least once a month as a result of an inability to fully analyze data. These are some of the findings in a new report from MeriTalk’s (a public-private partnership focused on improving the outcomes of government IT), Navigating the Cybersecurity Equation, which examines how agencies are using big data and advanced analytics to better understand cybersecurity trends and mitigate threats.
The survey asked 150 federal cybersecurity professionals to examine how agencies are using big data and analytics to better understand cybersecurity trends and mitigate threats. The study found that 81 percent of federal agencies say they’re using data analytics for cybersecurity in some capacity—53 percent are using it as a part of their overall cybersecurity strategy, and 28 percent are using it in a limited capacity. However, breaches continue to afflict agencies with 59 percent of federal agencies reporting they deal with a cybersecurity compromise at least once a month due to their inability to fully analyze data. In addition, just 45 percent found their efforts to be “highly effective.” What is holding agencies back from reaching their cybersecurity goals? Where do agencies go from here?
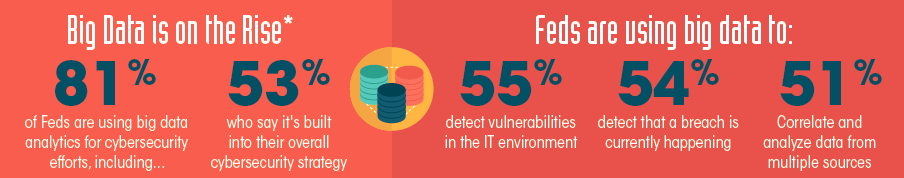
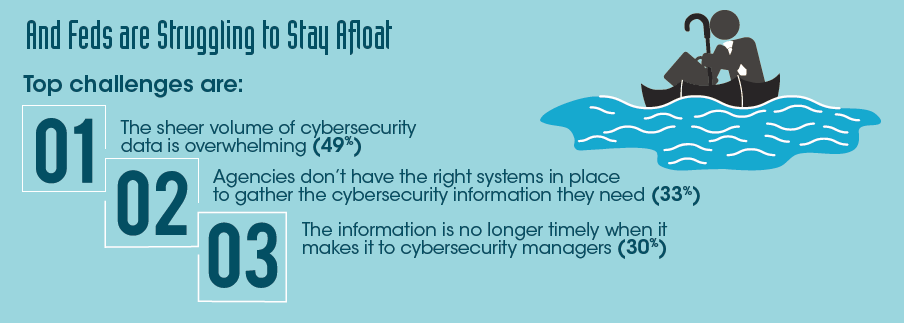
The top challenges for feds surrounding cybersecurity as reported by participants were:
- The sheer volume of cybersecurity data, which is overwhelming (49 percent)
- The absence of appropriate systems to gather necessary cybersecurity information (33 percent)
- The inability to provide timely information to cybersecurity managers (30 percent)
Because of these challenges, participants stated more than 40 percent of their data goes unanalyzed. Other obstacles include the lack of skilled personnel (40 percent), potential privacy concerns (27 percent), and lack of management support/awareness (26 percent).
From a perspective outside the U.S., cybersecurity has been identified as the number one threat to the UK government. The UK is seeing a big emphasis on using National Cyber Security Center (NCSC) that was announced early 2016. The UK faces a growing threat of cyberattacks from states, serious crime gangs, hacking groups as well as terrorists. The NCSC will help ensure that the people, public and private sector organizations and the critical national infrastructure of the UK are safer online.
Source: Navigating the Cybersecurity Equation by MeriTalk
Data analytics is playing a significant role in looking at the threat landscape—to determine where weaknesses are, and whether the right strategies and tools are in place. Additionally, there is a focus between the military and the intelligence services, which are centered on pursuing penetration testing. It is difficult to do penetration testing on live systems, and the challenge is that you’ll never really be able to test the vulnerabilities across the network for fear of bringing down critical applications. Dell EMC Cyber Solutions Group has been developing applications that enable penetration at a database level with zero impact on the database and provides real-time assessments across the network in seconds. As soon as these threats are identified, assessments can be announced to determine how fit the security solution is. The Cyber Solutions Group is part of Dell EMC, and features expertise in the realms of advanced storage technologies, high availability, cyber security, big data, cloud computing, and data science.
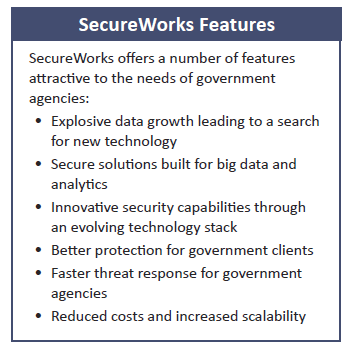 SecureWorks provides proven threat detection. Offered as a service, SecureWorks monitors the environment and looks for any kind of threats whether from the network, or internally, or externally. The reason SecureWorks is based on the Cloudera ApacheTM Hadoop® software platform is because the amount of attacks happening on a given environment is so high. It’s necessary to be able to monitor logs from network devices, logs from computers, notebooks, servers, etc. Typically, you don’t have anywhere to put all that log data, and you don’t have anything fast enough to process and analyze the data. Hadoop is an open source analytics platform, built from the ground up, to address today’s big data challenges. It enables government agencies to load and consolidate data from various sources into the highly scalable Hadoop Distributed File System (HDFS). This data can then be processed using highly distributed compute jobs through the MapReduce framework.
SecureWorks provides proven threat detection. Offered as a service, SecureWorks monitors the environment and looks for any kind of threats whether from the network, or internally, or externally. The reason SecureWorks is based on the Cloudera ApacheTM Hadoop® software platform is because the amount of attacks happening on a given environment is so high. It’s necessary to be able to monitor logs from network devices, logs from computers, notebooks, servers, etc. Typically, you don’t have anywhere to put all that log data, and you don’t have anything fast enough to process and analyze the data. Hadoop is an open source analytics platform, built from the ground up, to address today’s big data challenges. It enables government agencies to load and consolidate data from various sources into the highly scalable Hadoop Distributed File System (HDFS). This data can then be processed using highly distributed compute jobs through the MapReduce framework.
By integrating Hadoop with an IT environment, you’re able to achieve two important aspects. First, you’re able to solve the scalability problem—not in terms of infrastructure, but rather scalability as far as being able to detect a threat—a threat might be a log, a Trojan, something that came in through the firewall. So now you’re able to process and analyze that data in any given format and put it in Hadoop. Second, by putting your data in a single repository, like a data lake, you’re able to layer on statistical models and algorithms to detect anomalies and detect the threats on top of Hadoop. This enables you to build a single repository to do all your analysis—one way to ingest data, one way to process data, and one way to analyze data— to get an operational model of how you’re going to consume all the data and identify a threat.
Another cybersecurity solution is from RSA, also a part of Dell EMC Technologies. RSA security analytics was used by Los Angeles World Airports (LAWA) in order to track everything that happens within its environment. Working frequently with the FBI and the Secret Service, it has to be accountable for its cybersecurity. Its goal was to have real-time detection of security events in order to ensure public safety. RSA security analytics has enabled LAWA to greatly improve the speed of its response to immediate threats. The solution enables deepdive into payloads before and after a security event and delivers more information about each device than was previously possible. The RSA cybersecurity solution has also helped shorten incident response time as analysts can see all the information in one place, rather than spending time searching for it.
If you prefer, the complete insideBIGDATA Guide to Data Analytics in Government is available for download in PDF from the insideBIGDATA White Paper Library, courtesy of Dell EMC.





Speak Your Mind